GraphSpy in the Wild: Exposed Device Code Phishing Operation
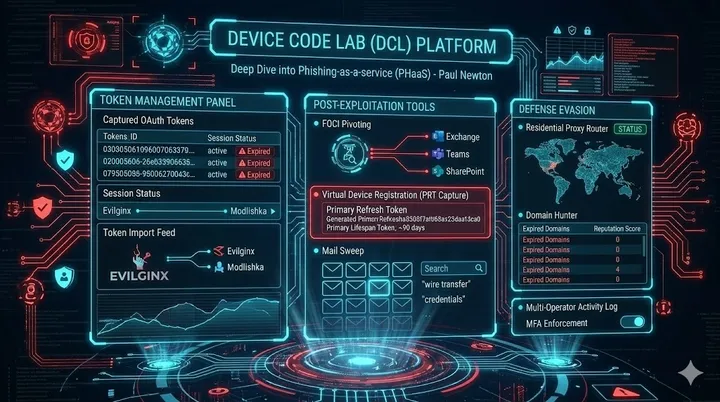
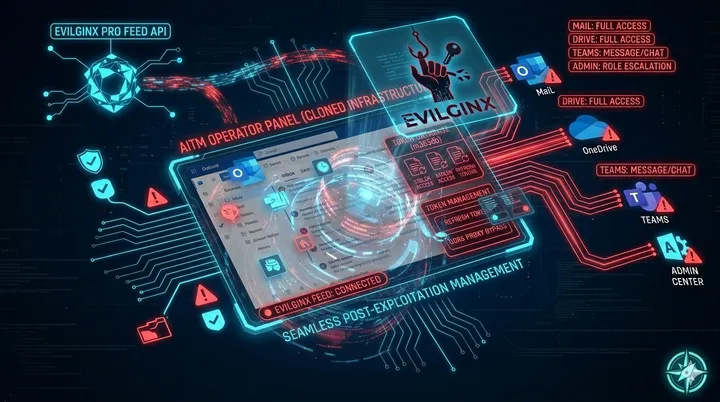
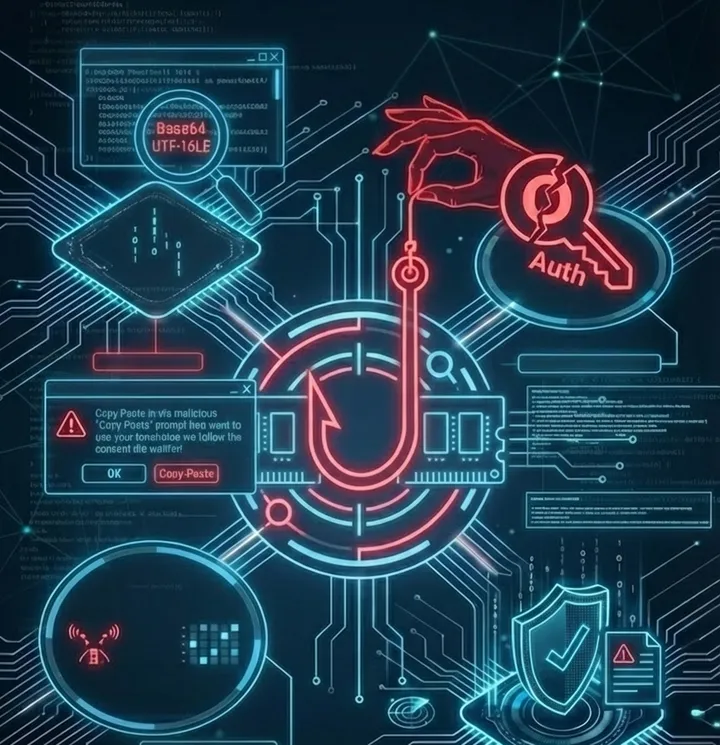
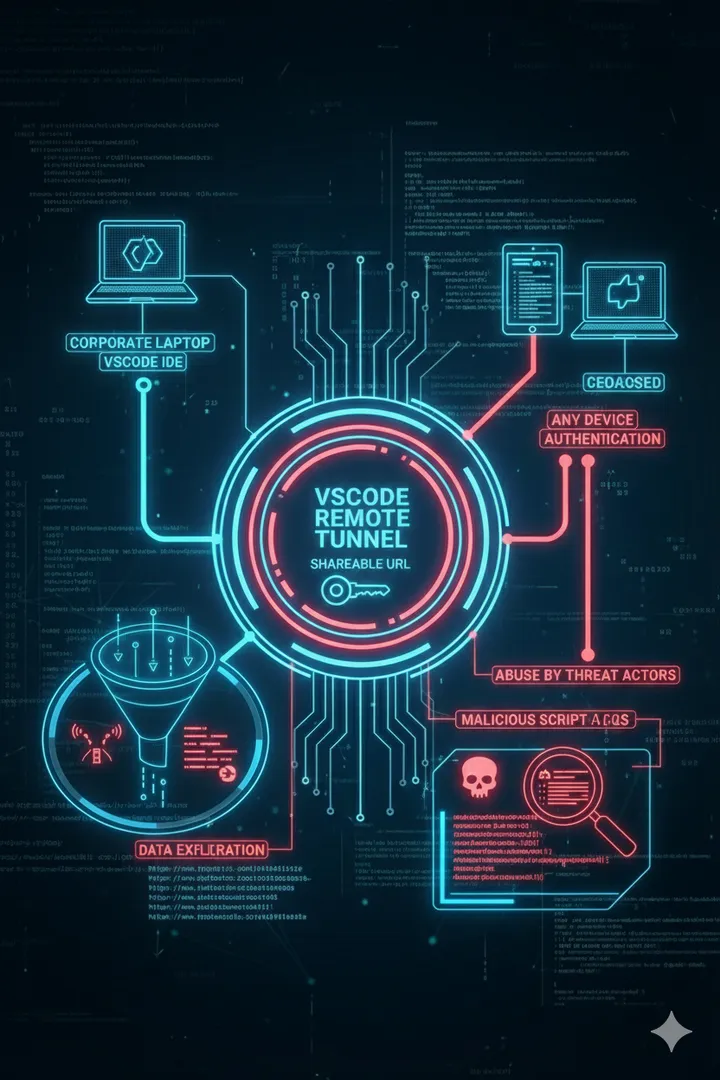
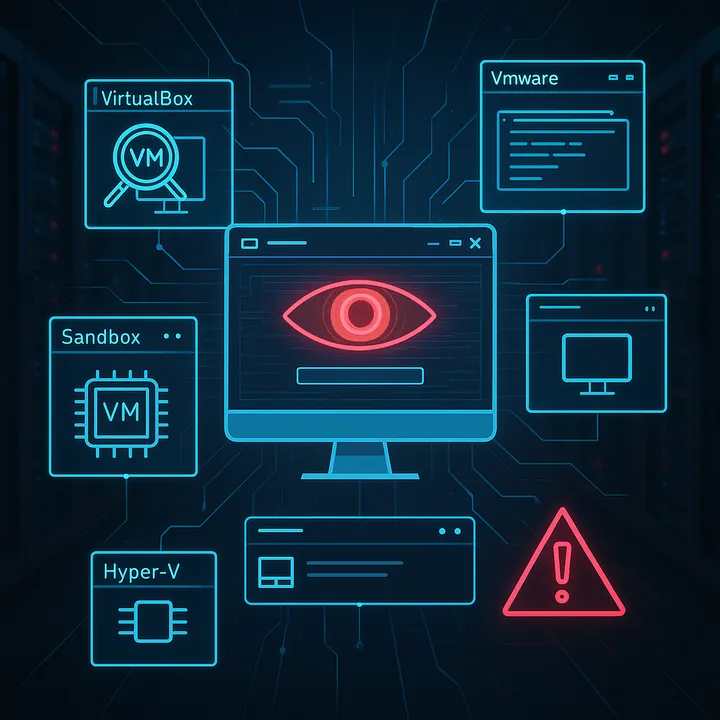
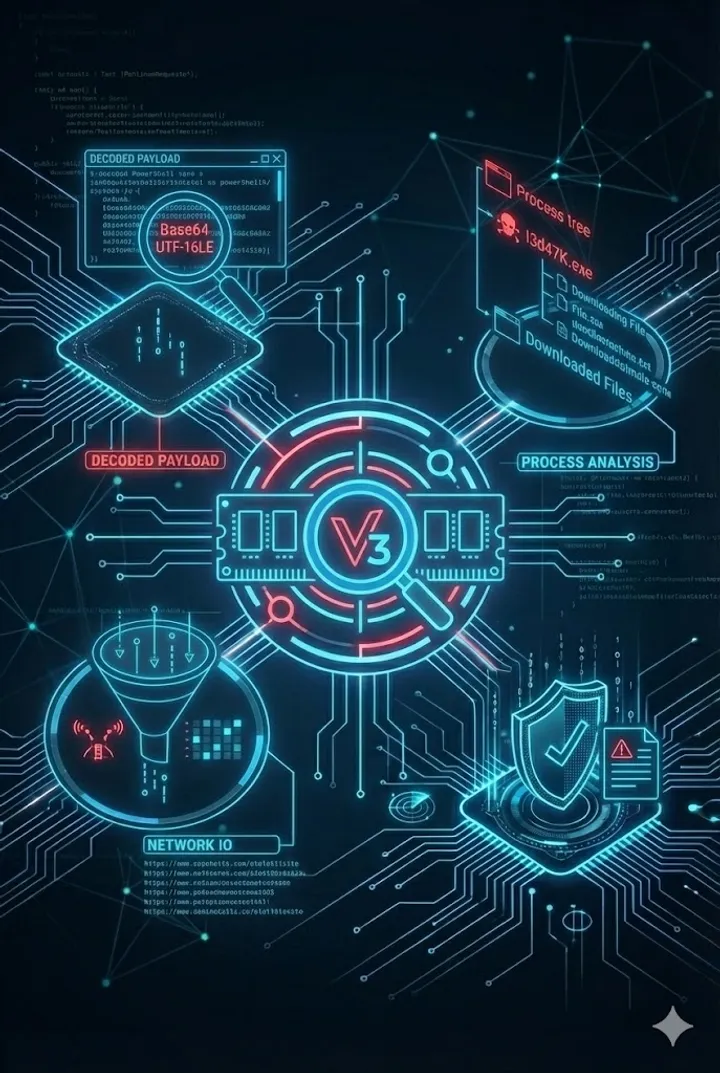
Analysis of a device code phishing operation built on the open-source GraphSpy tool, extended with a custom phish page generator and Cloudflare tunnel infrastructure, found via an exposed open directory and unauthenticated operator panel.